Introduction
Automated bot attacks pose an escalating threat to website security, capable of causing significant damage through:
- Data theft
- Denial-of-service incidents
- Fraudulent activities
As these malicious scripts grow increasingly sophisticated, website owners encounter the formidable challenge of protecting their digital assets. This article outlines essential steps for preventing bot attacks, including:
- Identifying harmful bots
- Implementing robust protective measures
By equipping readers with the necessary knowledge, we aim to help them fortify their online presence against these persistent threats. How can businesses effectively navigate this complex landscape and ensure their websites remain secure amid evolving bot tactics?
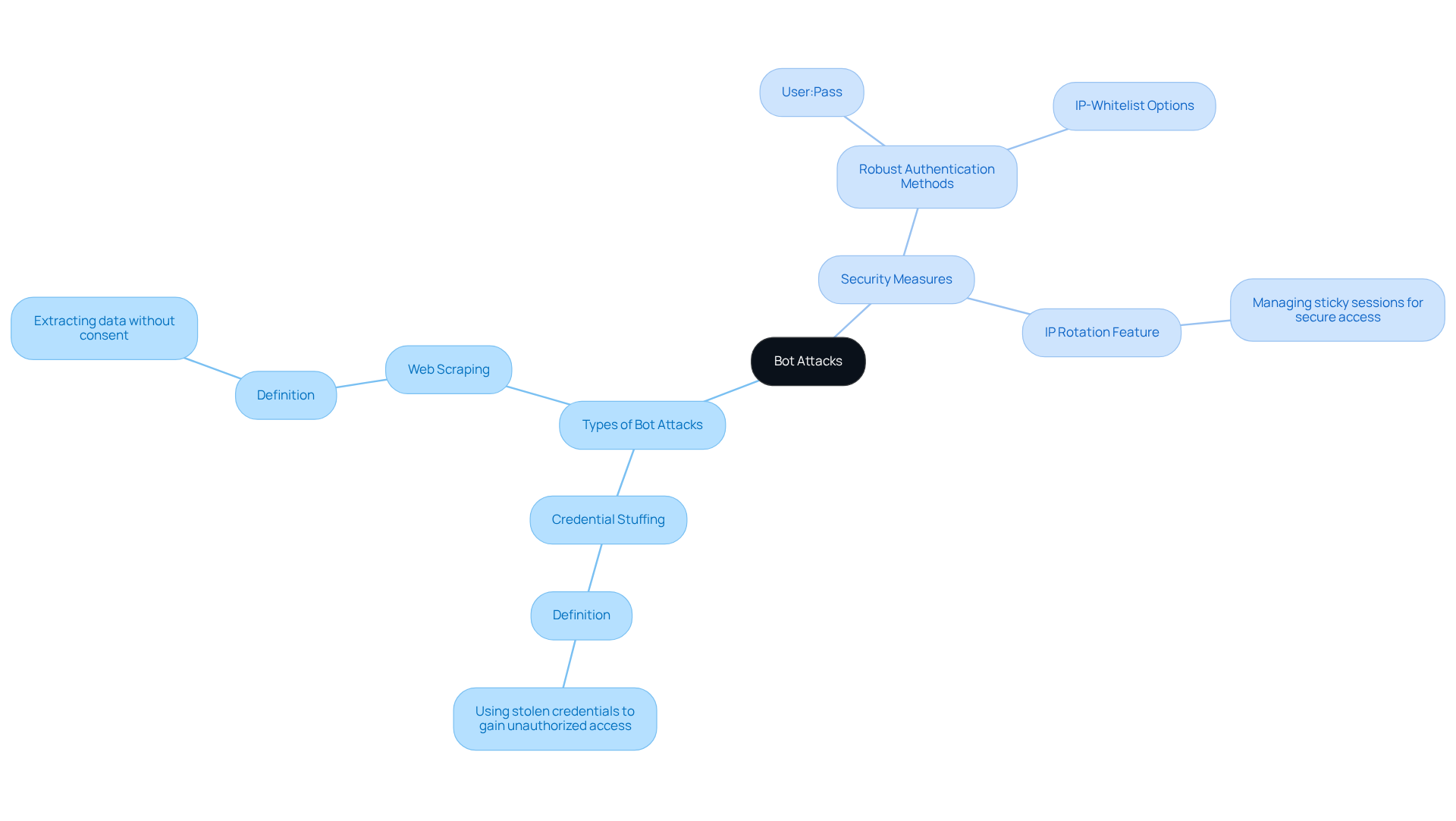
Understand Bot Attacks: Definition and Risks
Bot assaults are designed to execute harmful activities on online platforms. These activities include data scraping, incidents, and fraudulent transactions. Such assaults can significantly disrupt website functionality, compromise sensitive data, and result in substantial financial losses.
Among the most common types of bot attacks are:
- Credential stuffing
Credential stuffing involves bots using stolen credentials to gain unauthorised access, while entails extracting data without consent. Both pose serious threats to online security.
To combat these threats, implements , such as user:pass or IP-whitelist options, ensuring secure access to its services. Furthermore, 's built-in enhances security by managing sticky sessions that last up to 10 minutes. This allows for efficient data handling while minimising the risk of unauthorised access.
Understanding these threats and applying is essential for learning how to and from potential harm.
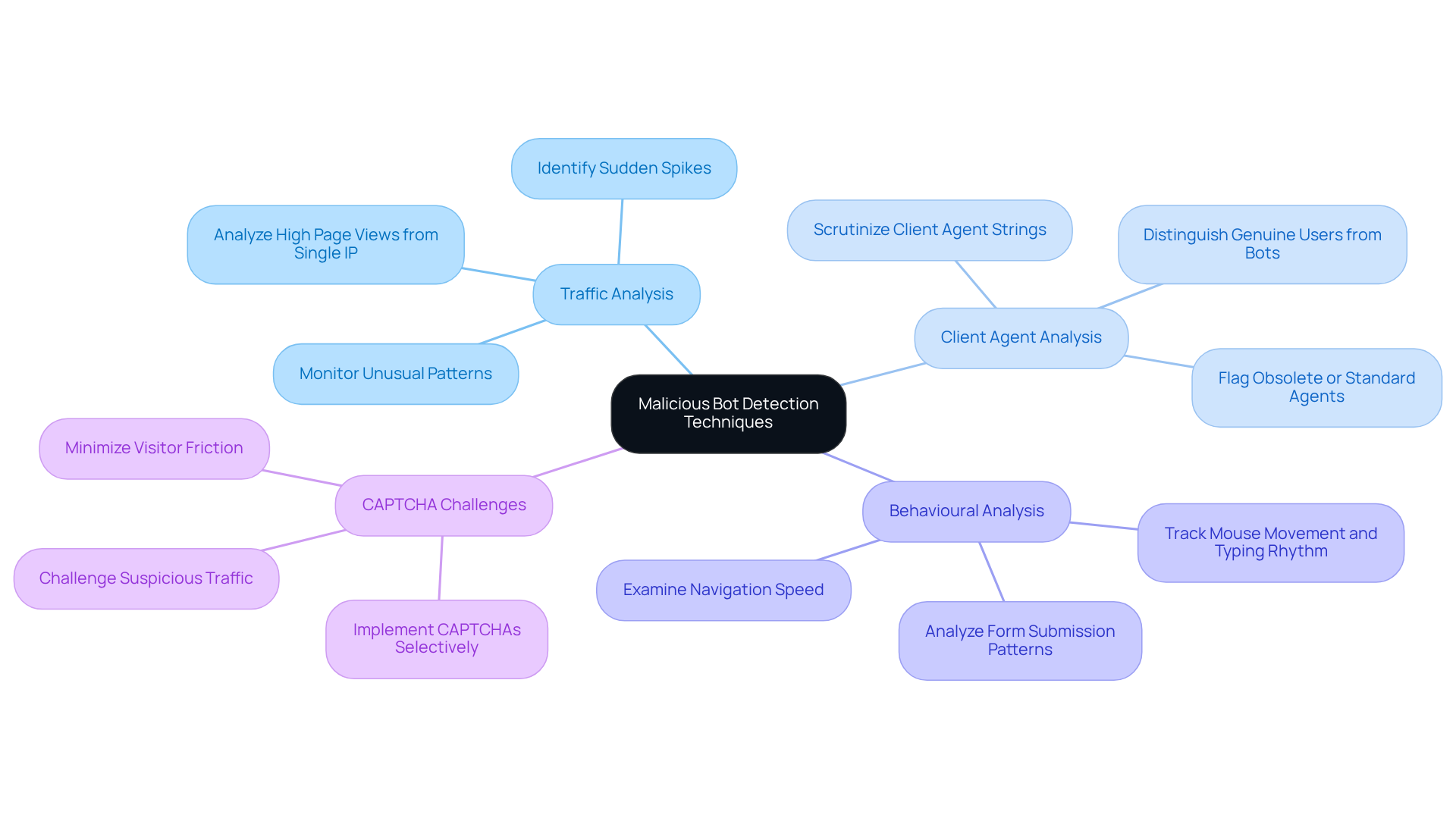
Identify Malicious Bots: Detection Techniques
To effectively identify malicious bots, website owners can employ several detection techniques:
- Traffic Analysis: Regularly monitor website traffic for , such as sudden spikes in requests or high page views from a single IP address. Almost one-third of all internet traffic consists of , making this analysis essential for early detection (ClickGuard Team).
- Client Agent Analysis: Scrutinise the client agent strings of incoming requests. Numerous bots utilise obsolete or standard agents, which can be flagged for further investigation. This method assists in distinguishing between genuine individuals and automated scripts (Nanhi Singh).
- : Examine behaviour for anomalies, such as rapid navigation through pages or excessive form submissions. Behavioural signals, including mouse movement and typing rhythm, can indicate non-human interactions, as bots frequently display patterns that differ significantly from human participants (ClickGuard Team).
- : Implement CAPTCHAs selectively to challenge suspicious traffic. Bots typically struggle with these tests, making them an effective barrier against automated submissions. By applying CAPTCHAs only to high-risk sessions, site owners can minimise visitor friction while maintaining security (Risk-Based CAPTCHA case study).
By employing these techniques, owners can effectively learn , , preserving the integrity of their analytics and ensuring a better user experience. Additionally, it's important to note that every click from a bot results in zero chance of conversion, emphasising the need for robust detection methods (ClickGuard Team).
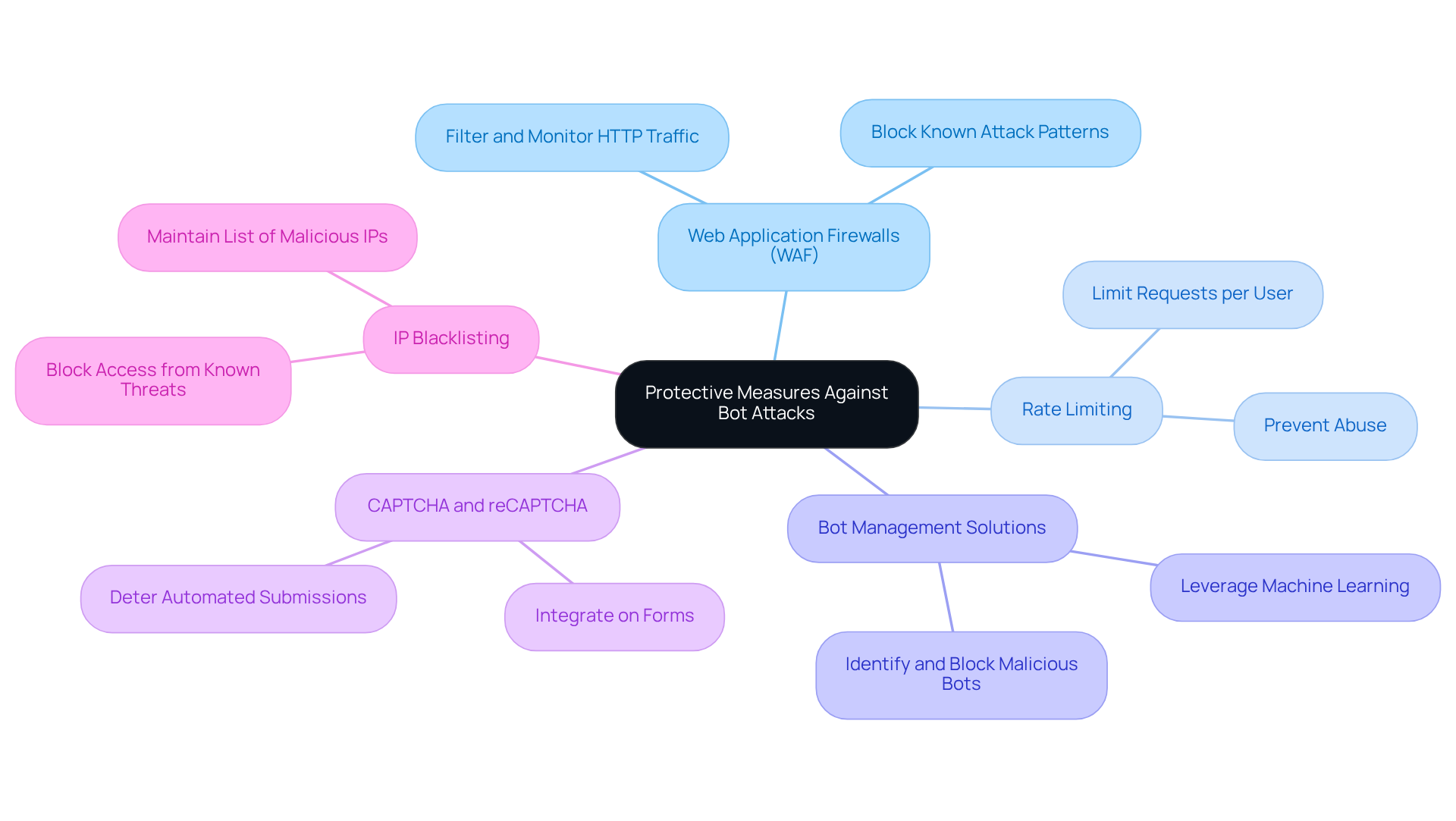
Implement Protective Measures: Tools and Techniques
To protect your website from , consider implementing the following measures:
- : Deploy a WAF to , effectively blocking known attack patterns.
- : Set limits on the number of requests a user can make within a specified timeframe to prevent abuse.
- : Utilise dedicated bot management tools that leverage machine learning to identify and block malicious bots.
- : Integrate CAPTCHA challenges on forms and login pages to deter .
- : Maintain a list of known and block them from accessing your site.
By adopting these protective measures, you can significantly enhance your site's defenses and learn how to stop bot attack on website.
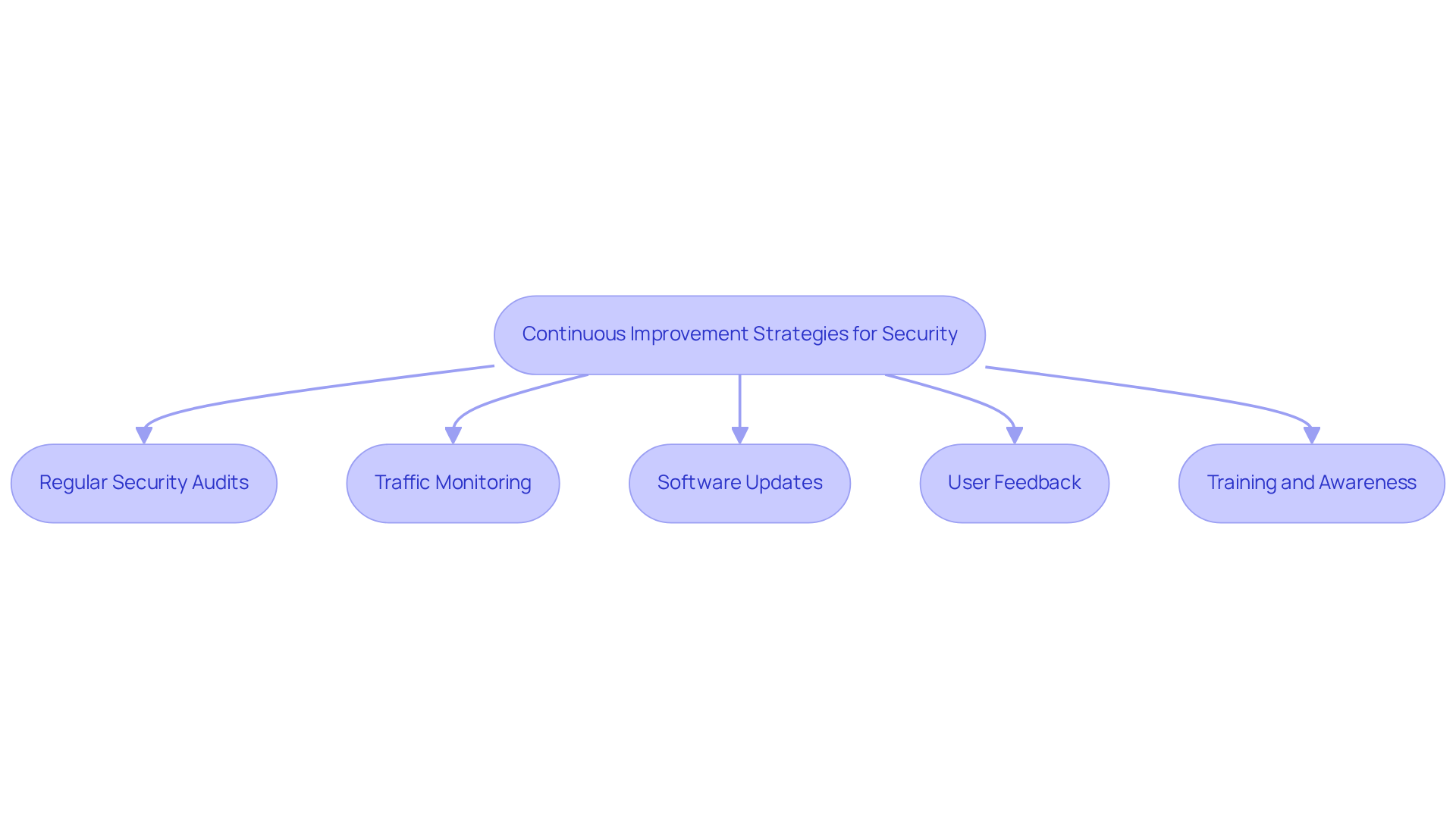
Monitor and Update Security: Continuous Improvement Strategies
To ensure your against bot attacks, consider implementing the following :
- : Conduct periodic audits of your website's to identify vulnerabilities and areas for improvement.
- : Continuously monitor traffic patterns to detect anomalies that may indicate bot activity.
- : Keep all software, plugins, and security tools up to date to protect against known vulnerabilities.
- : Encourage users to report suspicious activity or issues they encounter, providing valuable insights into potential bot threats.
- : Educate your team about the latest bot threats and security best practices to foster a culture of vigilance.
By adopting these strategies, you can understand how to on your website and maintain a strong defense against evolving threats.
Conclusion
In conclusion, bot attacks pose a significant threat to website security, capable of disrupting operations and compromising sensitive information. Understanding these automated threats and implementing effective protective measures is essential for maintaining a secure online presence. By taking proactive steps, website owners can significantly reduce the risk of bot-related incidents and safeguard their digital assets.
This article has outlined various types of bot attacks, including credential stuffing and web scraping, while emphasising the importance of robust detection techniques such as traffic analysis and behavioural monitoring. Additionally, it has provided a comprehensive overview of protective measures, including the use of web application firewalls, rate limiting, and bot management solutions. Regular security audits and continuous improvement strategies further enhance defences against evolving threats.
Ultimately, the fight against bot attacks requires vigilance and adaptability. By implementing the strategies discussed, website owners can protect their platforms from malicious activities and ensure a safer experience for their users. Taking action now not only secures the website but also fosters trust and reliability in the digital landscape.
Frequently Asked Questions
What are bot attacks?
Bot attacks are automated scripts designed to perform harmful activities on online platforms, including data scraping, denial-of-service (DDoS) incidents, and fraudulent transactions.
What are the risks associated with bot attacks?
Bot attacks can disrupt website functionality, compromise sensitive data, and lead to significant financial losses.
What are the common types of bot attacks?
The most common types of bot attacks include credential stuffing and web scraping.
What is credential stuffing?
Credential stuffing is a type of bot attack where bots use stolen credentials to gain unauthorised access to accounts.
What is web scraping?
Web scraping is the process of extracting data from websites without consent, which poses serious threats to online security.
How does Appstractor combat bot attacks?
Appstractor combats bot attacks by implementing robust authentication methods, such as user:pass or IP-whitelist options, to ensure secure access to its services.
What is the purpose of Appstractor's IP rotation feature?
Appstractor's IP rotation feature enhances security by managing sticky sessions that last up to 10 minutes, allowing for efficient data handling while minimising the risk of unauthorised access.
Why is it important to understand bot attacks and security measures?
Understanding these threats and applying security measures is essential for stopping bot attacks on websites and safeguarding your online presence from potential harm.
List of Sources
- Understand Bot Attacks: Definition and Risks
- Top Cybersecurity Statistics for 2026 | Cobalt (https://cobalt.io/blog/top-cybersecurity-statistics-for-2026)
- RondoDox Botnet Exploits Critical React2Shell Flaw to Hijack IoT Devices and Web Servers (https://thehackernews.com/2026/01/rondodox-botnet-exploits-critical.html)
- 135% Surge: Inside the Holiday Bot Attacks of December 2025 (https://securityboulevard.com/2026/01/135-surge-inside-the-holiday-bot-attacks-of-december-2025)
- DDoS Protection Faces Fresh Challenges As Bot Traffic Reaches New Peak (https://itsecurityguru.org/2025/12/22/ddos-protection-fresh-challenges-bot-traffic-reaches-new-peak)
- ecommercenews.uk (https://ecommercenews.uk/story/ai-powered-bots-surge-by-300-challenging-digital-business)
- Identify Malicious Bots: Detection Techniques
- thalesgroup.com (https://thalesgroup.com/en/news-centre/press-releases/bots-now-make-nearly-half-all-internet-traffic-globally)
- 2024 Bad Bot Report | Resource Library (https://imperva.com/resources/resource-library/reports/2024-bad-bot-report)
- Bot Detection – Learn How to Detect Malicious Bots in 2026 (https://datadome.co/guides/bot-protection/bot-detection-how-to-identify-bot-traffic-to-your-website)
- clickguard.com (https://clickguard.com/blog/how-to-detect-and-stop-bot-traffic)
- Top 6 bot detection tools to try in 2026 - ActiveProspect (https://activeprospect.com/blog/bot-detection-tools)
- Implement Protective Measures: Tools and Techniques
- 200 Inspirational Cybersecurity Quotes [2026] (https://digitaldefynd.com/IQ/inspirational-cybersecurity-quotes)
- Cybersecurity Awareness Month Quotes and Commentary from Industry Experts in 2025 (https://solutionsreview.com/cybersecurity-awareness-month-quotes-and-commentary-from-industry-experts-in-2025)
- AI Bots Overtake the Web: Imperva 2025 Bad Bot Report (https://cpl.thalesgroup.com/blog/access-management/ai-bots-internet-traffic-imperva-2025-report)
- Bot Manager vs. WAF: Why You Actually Need Both | Radware Blog (https://radware.com/blog/application-protection/bot-manager-vs-waf-why-you-actually-need-both)
- Monitor and Update Security: Continuous Improvement Strategies
- Security Week Home (https://securityweek.com)
- kaspersky.com (https://kaspersky.com/blog/most-important-cybersecurity-resolutions-2026/55069)
- Cybersecurity Predictions for 2026: The Future of Digital Threats (https://darkreading.com/threat-intelligence/cybersecurity-predictions-for-2026-navigating-the-future-of-digital-threats)
- 110 security and compliance statistics for tech leaders to know in 2025 (https://vanta.com/resources/compliance-statistics)
- The Importance of Regular IT Security Audits – Ventrix IT (https://ventrixit.co.uk/the-importance-of-regular-it-security-audits)




